What is code quality? Code quality refers to the degree to which software code is readable, maintainable, secure, and free of defects. High-quality code follows consistent standards, is testable, and is structured so that any developer, not just the original author can understand, modify, and extend it without introducing new bugs. It is measured by metrics including cyclomatic complexity, test coverage, code duplication, and the density of static analysis warnings.
Why Code Quality Deserves Your Attention Right Now
Every software team wants to move fast. But speed without discipline creates a debt that compounds silently. According to a Gartner (2024) survey of 120 software engineering leaders, reducing technical debt ranked among the top strategic priorities alongside integrating AI and increasing developer productivity. That is not a coincidence. Poor code quality is the single largest driver of technical debt.
Poor code quality is the single largest driver of technical debt and the most preventable.
Learning how to improve code quality is no longer optional. It is a foundational skill that separates developers who ship maintainable products from those who accumulate liabilities their teams spend months paying back.
What Actually Makes Code High Quality?
High-quality code is readable, testable, and consistent. These three properties are not subjective; they map directly to measurable outcomes.
A 2023 study published in Empirical Software Engineering (Börstler et al.) surveyed developers across multiple countries and found that readability and structure were the most commonly cited properties of quality code. Documentation followed closely. Developers already know what good looks like the challenge is applying it consistently under deadline pressure.
In practice, teams building enterprise applications typically find that readability problems compound over time. A function named processData that grew from 30 lines to 300 lines over three years is not a documentation failure. It is an architecture failure, one that a linter or code review could have flagged early.
The core quality attributes to target are: low cyclomatic complexity, high test coverage, zero hardcoded secrets, minimal code duplication, and adherence to the team’s agreed style guide.
Static Analysis Tools: Your First Line of Defence
Static analysis tools scan your code before it runs, catching bugs, style violations, and security vulnerabilities at the earliest possible moment.
The most-used tools in this category include SonarQube, ESLint, and Pylint. SonarQube is trusted by over 7 million developers across 400,000 organisations globally (SonarSource, 2024). It supports more than 35 programming languages and integrates directly into CI/CD pipelines via GitHub Actions, GitLab CI, and Jenkins.
| Tool | Key Strength | Best Used When |
|---|---|---|
| SonarQube | Multi-language support (35+), security scanning, CI/CD quality gates | Enterprise teams needing unified quality and security oversight across large codebases |
| ESLint | Highly configurable JavaScript/TypeScript linting with plugin ecosystem | JavaScript/TypeScript projects requiring custom rule sets and real-time IDE feedback |
| Pylint | Deep Python static inference finds subtle bugs beyond surface-level style checks | Python teams that need thorough analysis and are willing to tune false-positive rates |
| CodeQL | Query-based vulnerability detection across entire repositories, fewer false positives | Teams using GitHub Advanced Security who need semantic code analysis for security-critical code |
Table 1: Comparison of leading static analysis and code quality tools.
ESLint has over 24,000 stars on GitHub and remains the dominant choice for JavaScript. Pylint is widely used in Python projects and uniquely performs type inference without requiring full type annotations.
Code Snippet 1: ESLint Configuration (.eslintrc.json)
Source: eslint/eslint – github.com/eslint/eslint
This configuration enforces three common quality rules: warn on unused variables (a frequent source of dead code), require strict equality checks (preventing type-coercion bugs), and flag console.log calls left in production builds. Placing this file at the project root activates these checks for every pull request via any CI pipeline that runs eslint ..
Static analysis finds the bugs your tests never run because the code paths were never even reachable.
Code Reviews: The Human Layer of Quality Control
Peer code review is the most cost-effective quality mechanism available to a software team and the most underused.
A 2024 paper in the Journal of Artificial Intelligence Research (O’Connor, 2024) examined code review practices across multiple organisations and found that teams practising regular peer reviews reported measurable improvements in both code quality and knowledge sharing. Reviewers who focus on logic correctness, naming clarity, and test completeness catch issues that static analysis cannot: architectural misalignments, missing business logic, and design decisions that are technically valid but strategically wrong.
A 2024 study on static analysis tools in secure code review (Charoenwet et al., arXiv:2407.12241) reinforced this point: static analysis tools and human reviewers are complementary, not interchangeable. Tools catch pattern-based issues; humans catch intent-based issues.
Teams building this typically find that the hardest part is not tooling, it is culture. Code review works when it is framed as collaborative improvement, not as approval gatekeeping. Setting a team norm of keeping pull requests under 400 lines of changed code dramatically reduces review fatigue and increases comment quality.
CI/CD Pipelines and Quality Gates: Automating the Standard
Automated quality gates in CI/CD pipelines enforce code standards on every commit, removing the human bottleneck from routine compliance checks.
SonarQube’s Quality Gate feature lets teams define pass/fail criteria, for example, no new critical vulnerabilities, test coverage above 80%, and zero newly introduced code smells, and block merges automatically when those thresholds are not met. G2 has ranked SonarQube the number one static analysis tool for five consecutive years (SonarSource, 2024).
According to McKinsey (2024), generative AI tools can help developers complete tasks up to twice as fast, but that speed advantage is only durable when quality gates prevent regressions from being merged. Teams that adopted AI coding assistants without updating their quality pipelines saw a 7.2 percent decrease in delivery stability, according to the Google DORA report (2024).
Speed without quality gates is just a faster way to accumulate technical debt.
Code Snippet 2: GitHub Actions Workflow for SonarQube Quality Gate
Source: SonarSource/sonarqube – github.com/SonarSource/sonarqube
yaml
name: Code Quality Check
on: [push, pull_request]
jobs:
sonar:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: SonarQube Scan
uses: SonarSource/sonarqube-scan-action@master
env:
SONAR_TOKEN: ${{ secrets.SONAR_TOKEN }}
SONAR_HOST_URL: ${{ secrets.SONAR_HOST_URL }}This GitHub Actions workflow triggers a SonarQube scan on every push and pull request. The SONAR_TOKEN authenticates the scan without exposing credentials. When configured with a Quality Gate, the pipeline will fail and block the merge if the code does not meet the team’s defined thresholds, enforcing standards automatically rather than relying on individual discipline.
Architecture of a Quality-First Development Pipeline
A quality-first pipeline integrates checks at every stage of development from the developer’s IDE through to production deployment.
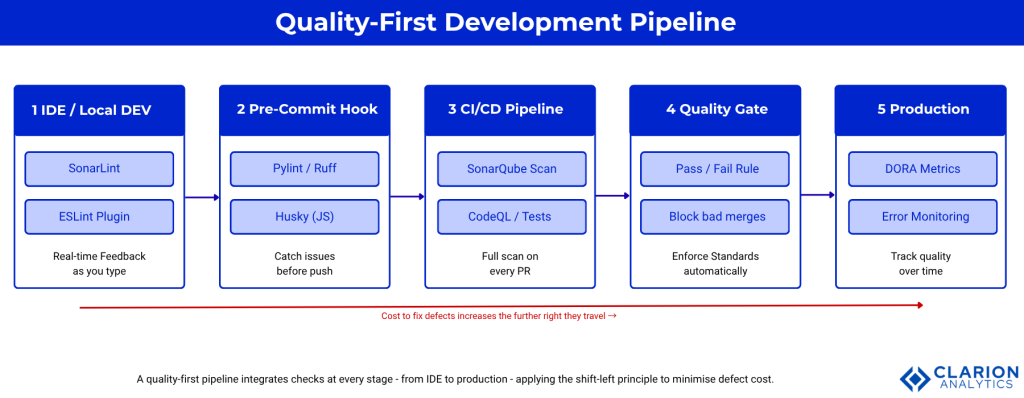
Figure 1: A quality-first development pipeline integrates static analysis at the IDE level (SonarLint, ESLint), pre-commit hooks (Pylint, Ruff), CI/CD scans (SonarQube, CodeQL), automated quality gates that block failing merges, and post-deployment monitoring. Each stage provides faster, cheaper defect detection than the stage after it. Cost to fix defects increases significantly as issues travel further right in the pipeline.
The pipeline has five layers. In the IDE, tools like SonarLint and ESLint provide real-time feedback as developers type. At the pre-commit stage, hooks run linters locally to catch issues before they ever reach the remote repository. On pull request creation, CI/CD pipelines execute full static analysis, automated tests, and security scans. A Quality Gate evaluates the aggregate results and blocks merges that fail. Post-merge, monitoring tools track metrics over time.
This architecture reflects the shift-left principle: catching defects earlier is always cheaper than finding them later. A bug found in the IDE costs minutes to fix. The same bug found in production can cost days of incident response.
A defect caught in the IDE costs a minute. The same defect caught in production costs a day.
How to Implement Code Quality Improvements: A Practical Guide
Start with the highest-impact, lowest-friction changes first and build the habit before adding complexity.
Step one is adding a linter to your IDE. Install the SonarQube for IDE extension in VS Code or IntelliJ. This takes under five minutes and gives every developer on your team real-time quality feedback with zero CI/CD changes required.
Step two is adding a pre-commit hook. Tools like Husky (for JavaScript/TypeScript projects) and pre-commit (for Python) run linters locally before any commit reaches the remote repository. This prevents low-quality code from entering the shared codebase at all.
Step three is adding a CI/CD quality check. A basic ESLint or SonarQube scan in a GitHub Actions workflow (see Code Snippet 2 above) is sufficient to start. Define your quality gate criteria gradually, begin with blocking only on critical-severity issues, then tighten thresholds as the team builds confidence.
Step four is establishing a code review checklist. A short, shared document covering the top five things reviewers should check, naming clarity, test coverage for new code, no hardcoded secrets, no new code smells, architectural consistency reduces review variability and speeds up the process.
Code quality and code security are not separate disciplines; they are two sides of the same engineering standard.
Frequently Asked Questions About Code Quality
What is code quality, and why does it matter for developers?
Code quality is the measure of how readable, maintainable, secure, and defect-free a codebase is. It matters because low-quality code accumulates technical debt that slows future development, increases bug rates, and raises the cost of onboarding new team members. High-quality code is faster to extend, easier to test, and less likely to fail under production conditions.
What are the best static analysis tools for improving code quality?
SonarQube is the most widely adopted platform, supporting 35+ languages with integrated security scanning and CI/CD quality gates. ESLint is the leading tool for JavaScript and TypeScript. Pylint provides deep Python analysis. CodeQL is a strong choice for GitHub-hosted repositories needing semantic security analysis. The best tool is the one your team will actually use consistently.
How does code review improve code quality?
Peer code review exposes logic errors, poor naming, missing tests, and architectural misalignments that automated tools cannot detect. Reviewers bring domain knowledge and design intent to the evaluation. Research published in 2024 confirms that regular peer review measurably improves quality metrics and accelerates knowledge sharing across teams. Short pull requests under 400 lines produce higher-quality reviews.
How do I set up a code quality gate in my CI/CD pipeline?
Add a SonarQube scan step to your GitHub Actions, GitLab CI, or Jenkins pipeline. Define a Quality Gate in the SonarQube dashboard specifying minimum test coverage, maximum critical issues, and duplication limits. Configure the pipeline to fail the build when the gate is not passed. Start with permissive thresholds and tighten them over one to two sprint cycles as the team adapts.
What is the difference between code quality and code security?
Code quality covers readability, maintainability, and structural correctness. Code security specifically targets vulnerabilities, SQL injection, hardcoded credentials, insecure deserialization, and similar exploitable flaws. In practice, they overlap: high-quality code is inherently easier to audit for security issues, and tools like SonarQube and CodeQL address both dimensions simultaneously.
Conclusion: Three Things That Will Transform Your Codebase
Three insights from this guide are worth internalising. First, quality must be automated to be consistent; relying on individual discipline without tooling is a system designed to fail under deadline pressure. Second, static analysis and peer code review are complementary: tools catch pattern violations; humans catch intent violations. Third, the shift-left principle pays compounding returns; every defect caught earlier in the pipeline is cheaper to fix and less likely to reach production.
The question worth sitting with: what is one quality gate your team could add to your pipeline this sprint that you could not remove next sprint?