DEFINITION – Node.js Security Best Practices
Node.js security best practices are a set of layered controls applied to JavaScript server-side applications to prevent unauthorised access, data leakage, and dependency compromise. They span five domains: dependency hygiene, HTTP header hardening, authentication and authorisation, secrets management, and observability. Together, they form a defence-in-depth model that limits the blast radius of any single failure.
Why Node.js Security Is a First-Principle, Not an Afterthought
Node.js security best practices are not optional for any system handling real user data. Sonatype’s 2024 State of the Software Supply Chain found that supply-chain attacks against npm doubled again in 2024, a trend that has repeated every year since 2019. Snyk’s 2024 Open Source Security Report found that 45% of organisations had to replace vulnerable build components in production, meaning nearly half of all Node.js deployment pipelines have shipped known-vulnerable code.
The attack surface is specific to the Node.js runtime. JavaScript’s prototype-based inheritance creates a vulnerability class, prototype pollution, that does not exist in most other server languages. A 2023 USENIX Security paper found 11 universal gadgets in core Node.js APIs alone that can be chained with prototype pollution to achieve Remote Code Execution without any additional libraries.
Teams building production Node.js services face three concrete risks: a compromised npm dependency shipped silently through a CI/CD pipeline, a misconfigured HTTP header exposing the application to clickjacking or XSS, and a hard-coded secret leaked to a public repository. This post addresses all three with specific, tested controls.
“Supply-chain attacks on npm doubled in 2024. Every unaudited dependency is an unsigned cheque written to an unknown payee.”
Lock Down Your Dependency Supply Chain
Dependency management is the highest-leverage security action for most Node.js teams. Malicious npm packages surged from 38 reports in 2018 to over 2,168 in 2024 according to arXiv research published in 2025, representing a 57x increase in six years.
Run npm audit in every CI pipeline, not just locally. Lock dependencies with npm ci --frozen-lockfile to prevent silent upgrades. Integrate Snyk or Dependabot to surface transitive vulnerabilities that npm audit misses. Strip dev-dependencies from production Docker images using multi-stage builds with npm ci --omit=dev.
Generate and maintain a Software Bill of Materials (SBOM) for every release. The Sonatype Open Source Malware Index Q4 2025 blocked 120,612 attacks in a single quarter, the vast majority against npm. An SBOM gives your incident-response team a two-minute map of exposure when the next worm surfaces.
“An unreviewed npm install is an open door. Treat every dependency as third-party code because it is.”
Harden the HTTP Layer with Headers, Rate Limiting, and TLS
HTTP header hardening is the fastest win available to any Node.js team. Helmet.js sets 13 security response headers with a single middleware line, including Content-Security-Policy, Strict-Transport-Security, and X-Frame-Options. With over 10,700 GitHub stars and 8.4 million weekly npm downloads, it is the de-facto standard perimeter control for Express applications.
Code Snippet 1: Helmet.js + Rate Limiting Initialisation
Source: helmetjs/helmet — README.md
This snippet pairs Helmet.js with express-rate-limit to address the two most common perimeter failures: missing security headers and unthrottled endpoints. Together, they block clickjacking, XSS header-injection, and brute-force credential stuffing without writing a single custom rule. Teams new to Node.js production security should add both before any other change.
Enforce TLS 1.3 at the load-balancer or reverse proxy layer (nginx, AWS ALB). Never terminate TLS inside the Node.js process in production. Set HSTS max-age to at least 31,536,000 seconds (one year) and include subdomains.
Authentication, Authorisation, and Input Validation
Authentication failures and injection attacks are the top two causes of Node.js application breaches. Both are preventable with established patterns; the failure is almost always implementation, not lack of available tools.
Use bcrypt or Argon2 for password hashing never SHA-256 or MD5. Issue short-lived JWTs (15-60 minutes) signed with RS256. Rotate signing keys via a JWKS endpoint so key compromise does not require a service deployment. Enforce role-based access control (RBAC) as middleware, not inline in route handlers.
Input validation must run server-side always. Use joi or zod to define explicit schemas and reject unknown fields. The OWASP Node.js Cheat Sheet recommends an allow-list approach: validate input against a known-good schema rather than trying to escape or sanitise unknown input.
Code Snippet 2: Parameterised Queries to Prevent SQL Injection
Source: OWASP Node.js Security Cheat Sheet
Parameterised queries are the single most effective control against SQL injection, a vulnerability that appears in roughly 60% of Node.js advisory reports mapped to OWASP Top 3 risks. The driver binds req.body.email as a literal value, not as SQL text, regardless of its contents.
“Input validation is not a UI problem. Every value that crosses a trust boundary must be validated server-side before it touches a data store.”
Secrets Management and Runtime Hardening
Hard-coded credentials are the number-one source of avoidable Node.js production breaches. A secret committed to a repository, even a private one, persists in git history, CI logs, and Docker image layers even after deletion.
Store secrets in a dedicated secrets manager: HashiCorp Vault, AWS Secrets Manager, or GCP Secret Manager. Inject values at runtime via environment variables, never read from .env files shipped with the container. Use pre-commit hooks (git-secrets, detect-secrets) to block accidental pushes. Vault’s dynamic secrets engine generates short-lived database credentials that expire automatically, eliminating the rotation burden entirely.
Run the Node.js process as a non-root user inside containers. Use the Node.js --permission flag (stable in Node.js 24) to restrict filesystem and network access at runtime. Always run the LTS release stream; the Active LTS line receives critical security patches; End-of-Life versions do not.
Observability: Logging, Error Handling, and Monitoring
Secure logging is the last line of defence when a breach does occur. Without structured, immutable logs, incident response is archaeology. Pino is the fastest structured logger for Node.js; it emits ndjson, integrates with ELK and Splunk, and has negligible overhead on high-throughput APIs.
Never log raw request bodies, passwords, tokens, or PII. Use Pino’s redact paths to strip sensitive fields before writing. Set NODE_ENV=production Express’s default error handler exposes stack traces in development mode. A production app must return generic error messages to clients while logging full detail internally.
In practice, teams building this typically find that centralised log shipping is already in place for infrastructure, but application-level audit trails are missing. Add a structured audit log for every authentication event, permission check, and data mutation, separate from the application debug log. Feed both into your SIEM. Set alerts on repeated auth failures, unusual access patterns, and unexpected outbound connections.
“An unmonitored Node.js app is not a secure Node.js app. Observability is not a DevOps concern; it is a security control.”
Architecture: Node.js Defence-in-Depth Security Model
The diagram below shows the five security layers and the components that compose each.
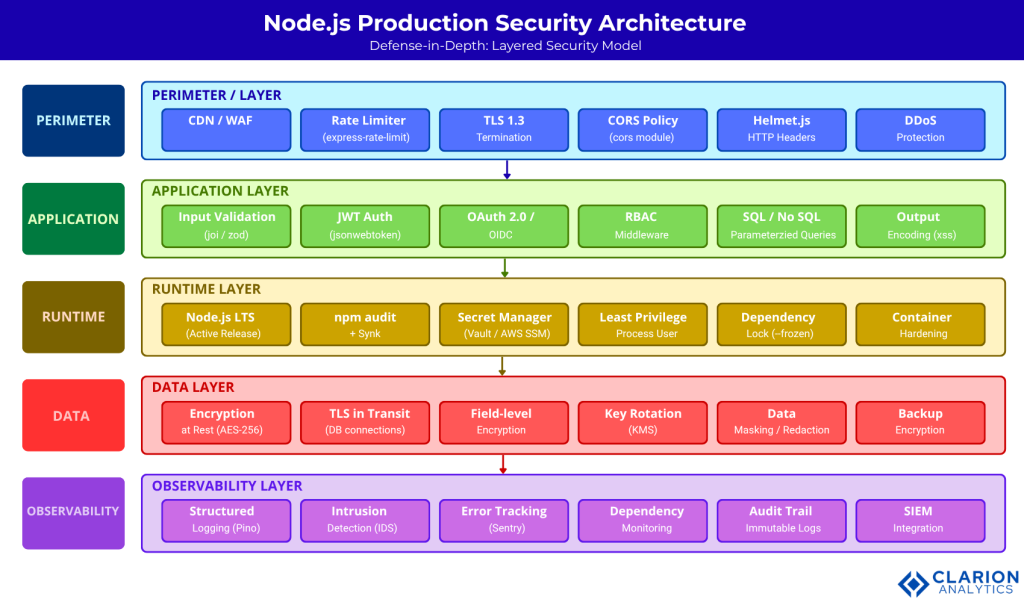
Figure 1. Traffic enters through the Perimeter Layer (CDN/WAF, rate limiting, TLS 1.3, Helmet.js headers), passes through the Application Layer (input validation, JWT auth, RBAC, parameterised queries), is hardened at the Runtime Layer (LTS Node.js, npm audit + Snyk, HashiCorp Vault, least-privilege process user), encrypted at rest and in transit at the Data Layer (AES-256, TLS for DB connections), and monitored end-to-end by the Observability Layer (Pino structured logs, Sentry, SIEM integration, immutable audit trail).
Tool Comparison: Selecting the Right Controls
| Option / Tool | Key Strength | Best Used When |
|---|---|---|
| Helmet.js | Sets 13 security HTTP headers in one call; zero-config start | Every Express app in production — perimeter header hardening |
| express-rate-limit | In-process rate limiting with flexible key strategies (IP, user, route) | Protecting auth endpoints and public APIs from brute-force and abuse |
| jsonwebtoken + JWKS | Stateless auth; supports RS256 key rotation via JWKS endpoints | Microservice architectures where sessions are impractical |
| Snyk / npm audit | Scans direct and transitive dependencies for known CVEs in CI/CD | Continuous integration pipelines; catches supply-chain vulnerabilities pre-deploy |
| HashiCorp Vault | Centralised secrets engine; supports dynamic credentials and audit logs | Teams managing multiple services with sensitive credentials across environments |
| Pino logger | Extremely fast structured JSON logging; ndjson format; low overhead | High-throughput APIs where Winston’s performance overhead is unacceptable |
Node.js Security FAQ
What is the most common security vulnerability in Node.js apps? Prototype pollution and insecure dependency management top the list. Prototype pollution allows attackers to inject properties into JavaScript object prototypes, enabling Denial of Service and Remote Code Execution. Insecure dependencies account for the majority of supply-chain breaches. Both are addressed by freezing prototypes and running automated dependency scanning in CI/CD.
How do I audit npm dependencies for security vulnerabilities? Run npm audit --audit-level=high in your CI pipeline to catch known CVEs in direct dependencies. Add Snyk or Dependabot for transitive dependency coverage and automatic pull-request remediation. Pipe both into your CI gate so a high-severity vulnerability blocks deployment.
Should I use JWT or sessions for Node.js authentication? JWTs with RS256 signing are preferred for microservice architectures where stateless validation is required. Use short expiry (15-60 minutes) with refresh tokens. Sessions are preferable for traditional monolithic apps where server-side revocation is needed. Never use HS256 with a symmetric secret shared across services.
What environment variables should I never store in my Node.js app? Never commit database credentials, JWT signing keys, API keys, or OAuth client secrets to source control. Store these in a secrets manager (Vault, AWS Secrets Manager) and inject at runtime. Use the .npmignore file to prevent secrets from being published to npm registries accidentally.
How does Helmet.js improve Node.js production security? Helmet.js sets 13 hardened HTTP response headers that Express does not set by default, including Content-Security-Policy, Strict-Transport-Security, and X-Frame-Options. Adding app.use(helmet()) takes under ten seconds and instantly hardens the perimeter against XSS, clickjacking, and MIME-sniffing attacks.
Conclusion: Three Principles to Carry Forward
Three principles emerge from the research and practice covered above. First, treat every npm dependency as third-party code because it is. Automated scanning in CI/CD, locked lock files, and SBOM generation are non-negotiable for any team shipping Node.js to production.
Second, security is a layered architecture problem. No single tool, not Helmet.js, not Snyk, not JWT, secures a production application alone. The defence-in-depth model illustrated above works because each layer limits the blast radius when the layer above it fails.
Third, observability is a security control. An application you cannot monitor is an application you cannot defend. Structured logs, centralised audit trails, and anomaly alerting close the feedback loop that converts a security posture from reactive to proactive.
What is the one control your team has not yet implemented? Start there.